Case B – Suspicious PowerShell Execution#
MITRE ATT&CK#
Tactic: Execution
Technique: T1059.001 – Command and Scripting Interpreter: PowerShell
This project demonstrates detection and investigation of suspicious PowerShell activity using Windows Security process creation logs and Splunk.
Scenario#
PowerShell execution was observed on a Windows endpoint from a standard user account. Because PowerShell is frequently abused by attackers for script execution, payload retrieval, and system reconnaissance, the activity was reviewed to determine whether the behavior represented legitimate administrative use or potentially malicious script execution.
Detection Logic#
This detection focuses on Windows Security Event ID 4688, which records process creation events. Monitoring process creation allows analysts to identify when potentially risky executables such as PowerShell are launched.
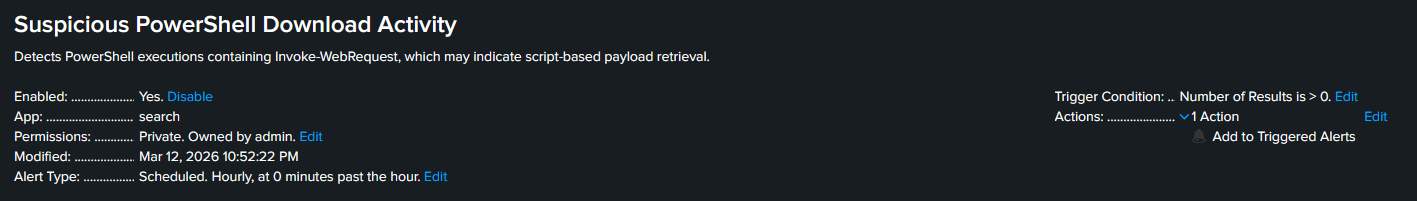
The Alert below uses the following Splunk query:
index=main sourcetype=WinEventLog EventCode=4688
PowerShell Invoke-WebRequestThe detection logic searches for PowerShell execution events that include the Invoke-WebRequest command, which can be used to retrieve files or scripts from external sources.
Trigger Simulation#
To generate the activity, a PowerShell command was executed on the victim machine from a standard user account. The command used the Invoke-WebRequest function to retrieve external content and write the output to a temporary file.
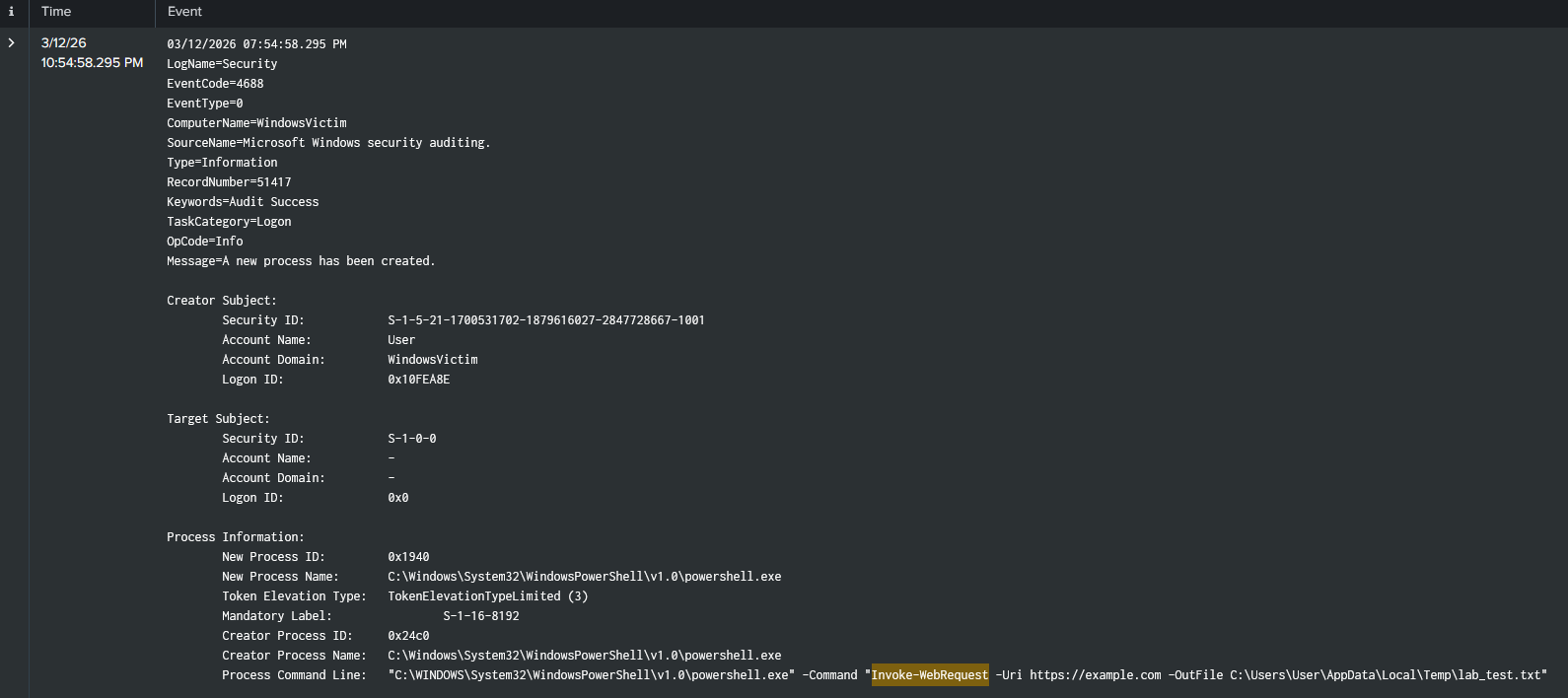
This action generated a Windows Security Event ID 4688, which recorded the execution of the PowerShell process and the associated command line.
Evidence#
Once the PowerShell execution occurred, the Splunk alert triggered and identified PowerShell activity containing the Invoke-WebRequest command on the WindowsVictim host.
The result below shows the Windows Security event associated with the triggered alert.
Investigation#
After validating the detection, the underlying event details were reviewed to determine the scope of the activity.
The process creation event confirmed that powershell.exe was executed on the host WindowsVictim by the user account User. The command line associated with the event contained the Invoke-WebRequest command, indicating that the PowerShell process attempted to retrieve external content.
Because PowerShell execution is commonly used by attackers to download and execute additional payloads, the command line was reviewed to determine the intent of the execution. No additional suspicious processes or follow-on activity were observed in this lab scenario.
Findings#
The investigation confirmed that a PowerShell process was executed on the host WindowsVictim using the Invoke-WebRequest command. The event was generated by a standard user account and recorded by Windows Security logging as Event ID 4688.
While the activity in this scenario was intentionally generated for testing purposes, similar behavior in a production environment could indicate script-based payload retrieval or other malicious PowerShell activity.
Remediation & Recommendations#
If similar activity were observed in a production environment, the endpoint generating the PowerShell command should be reviewed to determine whether the execution was legitimate or unauthorized.
Security teams should consider implementing additional monitoring for suspicious PowerShell commands and enabling enhanced PowerShell logging features such as script block logging and module logging. These controls provide greater visibility into PowerShell activity and improve the ability to detect malicious script execution.
Continued monitoring for unusual PowerShell usage patterns can help identify potential misuse of scripting tools commonly leveraged by attackers.